
New threads!


The modern approach to enterprise network management

DevNet Snack Minutes Episode #63!
I returned to The Art of Network Engineering Podcast!
Check it out!
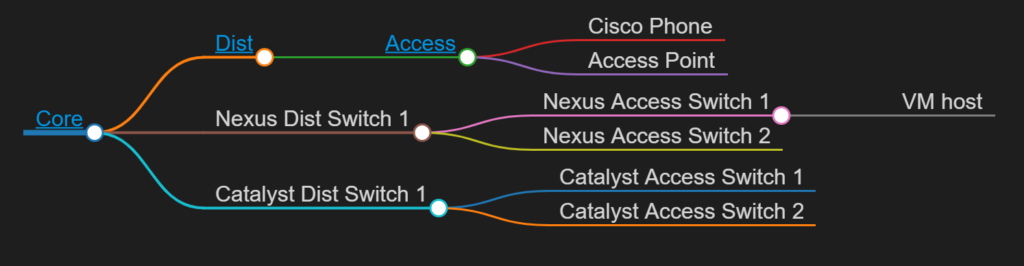
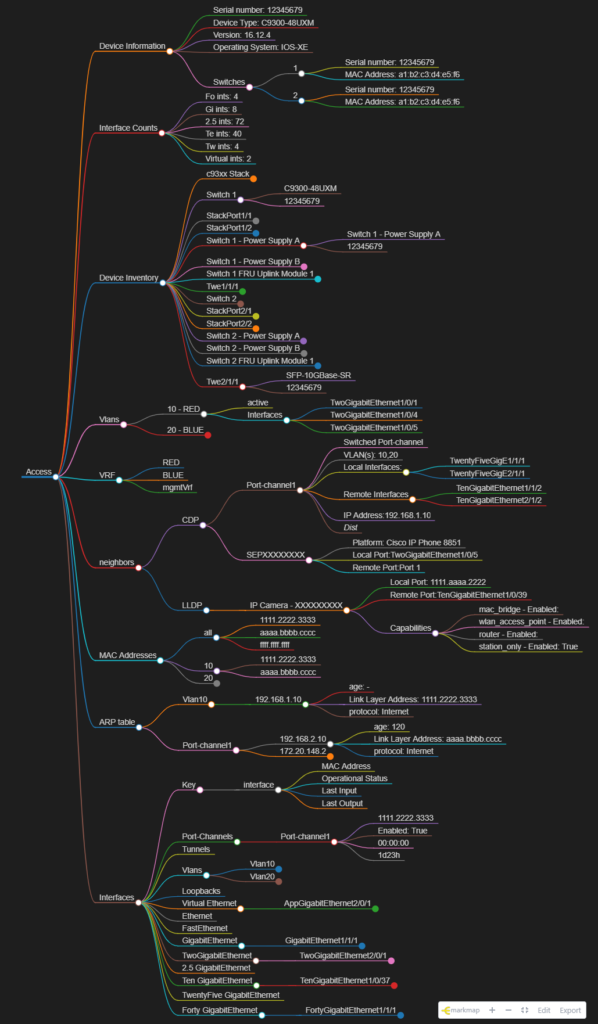
mind_nmap (this link opens in a new window) by automateyournetwork (this link opens in a new window)
An automated network Mind Map utility build from markmap.js.org
This was the most fun I’ve ever had on a podcast – I hope you enjoy it as much as I did!
Thank you to Cisco DevNet and everybody in my community who has supported me over the years!
I won!

I am so very happy to announce after 8 months of development Automate Your Network is now available on educative.io as an online course (early access) !
Automate Your Network – Learn Interactively (educative.io)

Check it out!
Infrastructure as Software – Applying A Software Design Pattern to Network Automation!
Applying A Software Design Pattern To Network Automation – Packet Pushers